Futures
Access hundreds of perpetual contracts
TradFi
Gold
One platform for global traditional assets
Options
Hot
Trade European-style vanilla options
Unified Account
Maximize your capital efficiency
Demo Trading
Introduction to Futures Trading
Learn the basics of futures trading
Futures Events
Join events to earn rewards
Demo Trading
Use virtual funds to practice risk-free trading
Launch
CandyDrop
Collect candies to earn airdrops
Launchpool
Quick staking, earn potential new tokens
HODLer Airdrop
Hold GT and get massive airdrops for free
Pre-IPOs
Unlock full access to global stock IPOs
Alpha Points
Trade on-chain assets and earn airdrops
Futures Points
Earn futures points and claim airdrop rewards
雲端託管平台 Vercel 遭駭!「DEX 前端」、「加密錢包介面」恐遭竄改劫財
Author: HIBIKI, Encrypted City
Cloud hosting platform Vercel hacked, crypto projects also rely on it
Vercel, a cloud hosting and deployment infrastructure platform, has confirmed that some internal systems were accessed without authorization, affecting a small number of customers.
Vercel offers serverless functions, edge computing, and continuous integration and deployment pipelines, and is well-known for the widely used React framework Next.js, many blockchain and cryptocurrency projects also depend on Vercel to deploy their front-end interfaces.
Vercel CEO Guillermo Rauch posted on social platform X explaining that the cause of this hacking incident was an issue with a third-party AI tool, Context.ai. A Google Workspace account of a Vercel employee was hijacked during a data leak incident on that AI platform, and the attacker subsequently used that account’s permissions to access Vercel’s internal environment.
All customer environment variables at Vercel are fully encrypted when static, and there is also a feature to designate variables as non-sensitive. The hacker obtained unencrypted, non-sensitive environment variables through enumeration.
Image source: Vercel official website | Vercel is a cloud hosting and deployment infrastructure, and many blockchain and crypto projects rely on Vercel to deploy front-end interfaces.
Hacker demands $2 million in ransom for stolen data
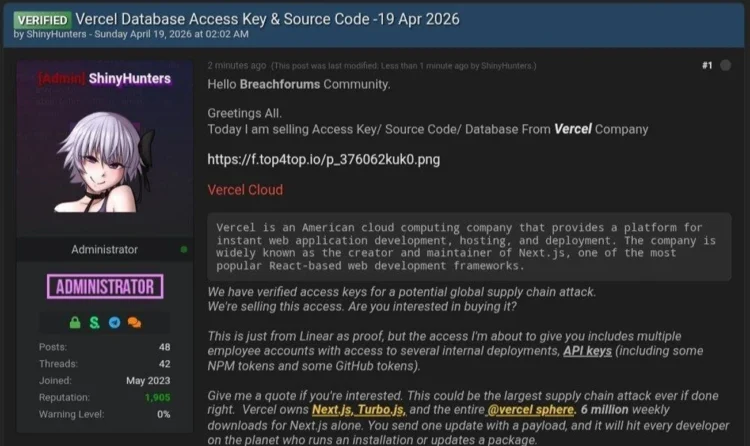
Security media Bleepingcomputer reports that a member claiming to be from the hacking group ShinyHunters posted on the hacking forum BreachForums, claiming to have obtained internal Vercel data and demanding $2 million in ransom.
The data shown by the hacker includes access keys, source code, database records, and internal deployment API keys for NPM and GitHub, even containing 580 Vercel employees’ names, emails, account statuses, and activity timestamps.
Image source: Breach Forums | Hacker offers $2 million to sell stolen data
However, members of the core ShinyHunters organization have denied involvement in this Vercel attack to the media, though the group previously attacked Rockstar, the developer of the GTA game series.
Vercel recommends a comprehensive review for customers
In response to this hacking incident, Vercel has hired external cybersecurity experts, reported to law enforcement, and launched updates to strengthen security management.
Vercel strongly advises administrators to check activity logs for suspicious behavior and urges Google Workspace admins to immediately verify whether any compromised OAuth applications are installed.
The company also recommends customers conduct a full review and replace environment variables, enabling the sensitive variables feature to ensure data is protected with static encryption.
Impacts of Vercel hacking on encrypted projects
This incident poses significant risks to the cryptocurrency industry. According to The Block, blockchain projects often deploy wallet interfaces, decentralized exchange (DEX) front-ends, and decentralized app (dApp) dashboards on Vercel.
If blockchain projects store private RPC endpoints, third-party API keys, or wallet-related secrets in non-sensitive environment variables, these secrets are now very likely to have been leaked.
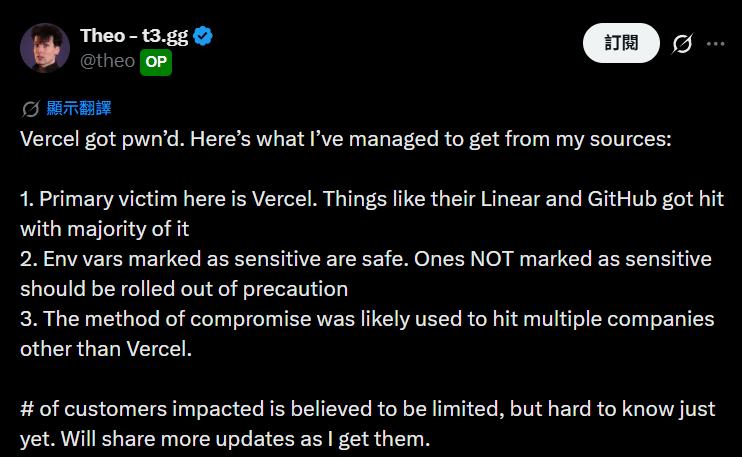
Notable community developer Theo Browne also posted that sources indicate the most severe impact was on Vercel’s internal Linear and GitHub integration systems.
Image source: X/Theo Browne
In the past, front-end security issues have frequently plagued the crypto space, with projects like CoW Swap, Aerodrome, and Velodrome experiencing domain hijacking incidents, which often involve redirecting visitors to phishing sites to steal assets.
The Block points out that this hacking incident occurred at the hosting and deployment layer, opening a new attack surface that completely bypasses domain system monitoring. In the worst case, attackers could directly tamper with the actual built front-end output of projects.