How does World ID work? In-depth analysis of the complete iris verification and Proof of Personhood process
As AI-generated content (AIGC) and automation tools become more widespread, the challenge of determining “who is a genuine user” online is growing increasingly complex. Traditional authentication methods—such as phone numbers, email, or verification codes—are no longer sufficient to prevent bots from mass registering or manipulating accounts. In this context, creating a mechanism to verify “real humans” has become a critical issue for Web3 and digital identity solutions.
World ID was introduced as an identity protocol to address this challenge. As a core part of the Worldcoin ecosystem, it leverages a combination of biometric and cryptographic technologies to achieve Proof of Personhood. This approach not only helps prevent Sybil Attacks but also offers a new pathway for implementing decentralized identity systems (DID).
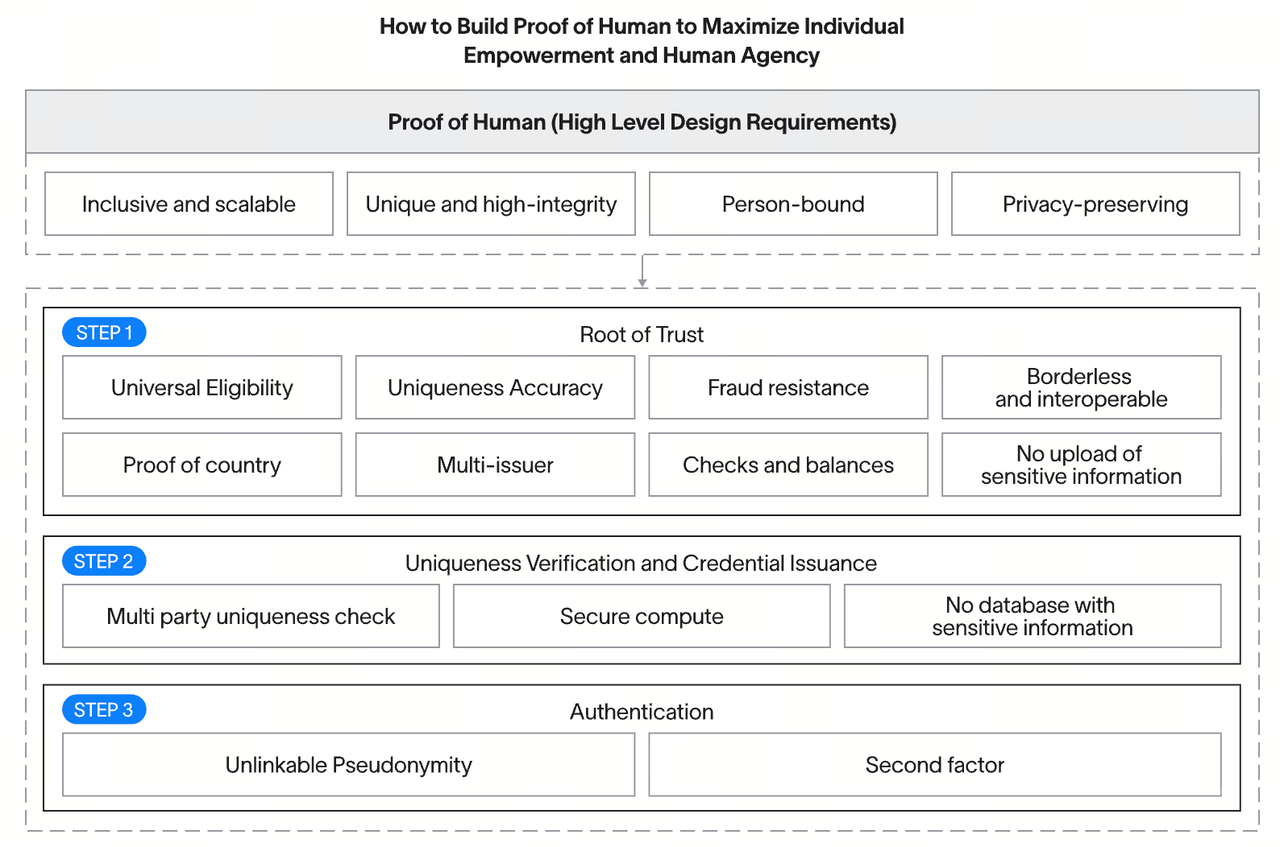
Image source: Worldcoin White Paper
What Is World ID?
World ID is a blockchain-based digital identity system designed to prove that a user is a “unique and real human being.” Unlike traditional identity systems, it does not rely on conventional personal information. Instead, it generates cryptographic credentials from biometric data, enabling users to authenticate themselves across multiple applications.
World ID differs from typical account systems by not directly storing users’ personal data. Rather, it generates a verifiable yet irreversible identity marker, ensuring both uniqueness and privacy protection.
What Are the Core Principles of World ID?
World ID is built on the concept of Proof of Personhood, ensuring that each identity is tied to a single real person. This is achieved through biometric recognition and cryptographic algorithms.
The system captures unique biometric data via iris scanning, converts it into a digital code, and then generates an encrypted hash value. Because each iris is highly distinctive, this method effectively prevents duplicate registrations and identity forgery.
Additionally, World ID uses Zero-Knowledge Proofs, allowing users to verify their identity without revealing specific biometric details—striking a balance between uniqueness and privacy.
How Does Iris Verification (Orb) Work?
World ID authentication relies on a specialized device called the Orb, which collects and processes users’ iris data.
During the process, users complete a one-time iris scan with the Orb. The device captures the iris image and converts it into a digital feature code, which is then processed into an IrisHash for identity generation.
A key aspect of this process is that the system does not retain the original image long-term—only the encrypted output is kept—significantly reducing the risk of sensitive data leaks.
What Is the Full World ID Verification Process?
From the user’s perspective, generating a World ID involves a multi-step, continuous process. Users first download the World App and create an account, then visit a location equipped with an Orb for identity verification.
After the iris scan, the system generates the corresponding IrisHash and uses cryptographic algorithms to create a unique World ID. This identity can then be linked to the user’s wallet for on-chain activities.
For future authentication, users can prove their identity with Zero-Knowledge Proofs, without needing to repeat the biometric process. This design enables identity reuse while minimizing repeated data exposure.
How Does World ID Protect User Privacy?
Privacy protection is central to World ID’s design. The system employs multiple technical measures to minimize reliance on sensitive data.
First, iris data is converted into a hash after capture, rather than storing the actual image. Second, Zero-Knowledge Proof technology allows users to verify themselves without revealing identity details. Additionally, the identity credential contains no directly identifiable personal information.
This architecture enables World ID to deliver unique identity verification while minimizing the risk of privacy breaches. However, real-world security depends on technical implementation and operational practices.
How Is World ID Different from Traditional KYC or DID?
World ID is fundamentally different from traditional KYC (Know Your Customer) and decentralized identity (DID) systems in its design philosophy.
KYC relies on government-issued documents and centralized databases, while DID emphasizes user control and portfolio management of data. In contrast, World ID focuses on verifying “whether you are a unique and real human,” rather than “who you are.”
This distinction makes World ID ideal for scenarios where duplicate identity prevention is critical—such as airdrop distribution, DAO voting, and anti-bot systems—while DID is better suited for identity presentation and data management.
Limitations and Challenges of World ID
While World ID introduces an innovative model for identity verification, it faces several challenges. Biometric technology is inherently sensitive, and user trust in data security will directly impact adoption.
The physical deployment of Orb devices also presents logistical hurdles, making global scaling a gradual process. Moreover, regional differences in biometric data regulations may affect adoption and expansion.
These factors collectively add to the uncertainties surrounding World ID’s real-world application.
Summary
By combining biometric and cryptographic technologies, World ID delivers Proof of Personhood—verifying that each real human has a unique identity in a decentralized environment. This mechanism provides foundational identity infrastructure for Web3, helping to prevent bot attacks and support equitable participation.
As AI technology continues to advance, the importance of robust identity verification will only grow. The approach pioneered by World ID offers a new direction for digital identity systems, though its long-term success will depend on balancing privacy, security, and regulatory compliance.
FAQs
What is World ID?
World ID is a digital identity protocol that verifies a user is a unique and real human being.
How does World ID work?
It uses the Orb to scan the iris, generates an IrisHash, creates an encrypted identity, and completes verification through Zero-Knowledge Proofs.
Does World ID store iris data?
The system does not store raw iris images; it represents identities using encrypted hashes.
What is Proof of Personhood?
Proof of Personhood is a mechanism to ensure each identity maps to a real human.
How is World ID different from KYC?
KYC verifies “who you are,” while World ID verifies “whether you are a unique human.”
Is World ID secure?
Security relies on cryptographic technology and privacy design, but device, data, and regulatory factors must also be considered.
Related Articles
Reshaping Web3 Community Reward Models with RWA Yields

An Overview of Musk's Love-Hate Relationship with DOGE

A Beginner's Guide to the SuperRare NFT Market

Gate Research: Exploring the SocialFi Landscape in 2024: Insights on the Path Forward, Market Trends, and Future Directions

Top 10 Chinese Crypto Podcasts for 2025